In the vast landscape of cyber threats, phishing remains one of the most pervasive and insidious forms of attack. Among the countless targets, Apple users have increasingly found themselves in the crosshairs of cybercriminals utilizing sophisticated techniques to lure unsuspecting victims into their traps. In this article, we’ll delve into the world of Apple phishing emails, exploring what they are, how they work, and most importantly, how you can protect yourself against them.
Understanding Apple Phishing Emails
Phishing emails are deceptive messages crafted to appear as if they’re from a legitimate source, such as Apple. These emails often contain urgent requests for personal information, such as login credentials, financial details, or other sensitive data. They typically employ various psychological tactics to induce panic or a sense of urgency, urging recipients to take immediate action to avoid supposed consequences.
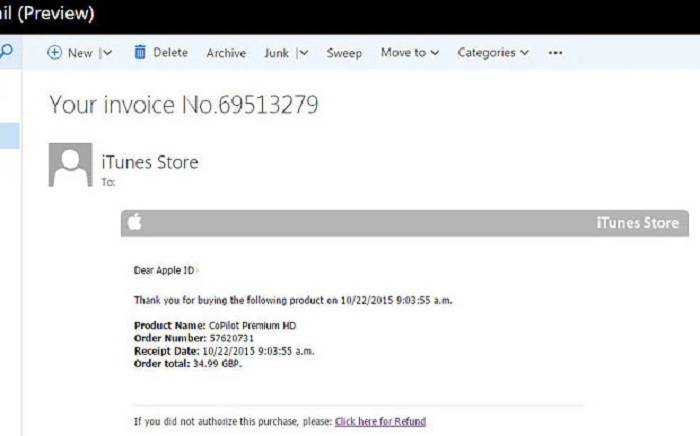
Apple phishing emails may claim that there’s been suspicious activity on your account, prompting you to verify your identity by clicking on a provided link. Alternatively, they might inform you of a supposed billing issue or an unauthorized purchase, coaxing you into providing payment information to resolve the matter swiftly. Regardless of the specific pretext, the ultimate goal is to trick you into divulging valuable information that can be exploited for malicious purposes.
Recognizing the Red Flags
While Apple phishing emails can be convincing, they often exhibit telltale signs that can help you identify them as fraudulent:
Sender’s Email Address: Check the sender’s email address carefully. Phishing emails often use addresses that mimic legitimate ones but contain subtle misspellings or variations.
Urgency and Threats: Beware of emails that pressure you to act urgently or threaten negative consequences for failing to comply. Legitimate companies typically don’t use such tactics.
Suspicious Links: Hover your mouse cursor over any links in the email (without clicking on them) to preview the destination URL. If the link seems unrelated to Apple’s official domain or appears suspicious in any way, avoid clicking on it.
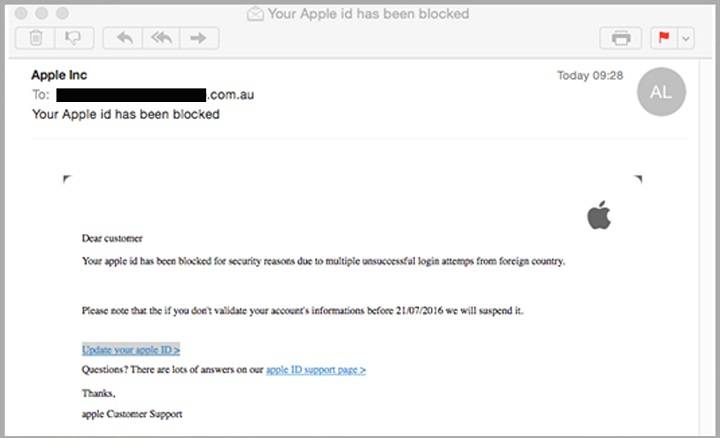
Generic Greetings: Phishing emails often use generic salutations like “Dear Customer” instead of addressing you by name, as legitimate communications from Apple would.
Poor Grammar and Spelling: Phishing emails frequently contain grammatical errors, spelling mistakes, or awkward phrasing. These errors can betray the fraudulent nature of the message.
Protecting Yourself Against Apple Phishing Emails
To safeguard yourself against the threat of Apple phishing emails, follow these proactive measures:
Verify Requests Independently: If you receive an email requesting sensitive information or urgent action, independently verify the request by directly visiting the official Apple website or contacting Apple’s customer support through trusted channels.
Enable Two-Factor Authentication (2FA): Enable 2FA for your Apple ID to add an extra layer of security. This ensures that even if your login credentials are compromised, unauthorized access to your account is significantly more difficult.
Educate Yourself and Others: Stay informed about the latest phishing techniques and educate yourself and your family members or colleagues about the red flags to watch out for. Awareness is a powerful defense against cyber threats.
Use Security Software: Install reputable antivirus and anti-phishing software on your devices to help detect and block malicious emails and websites.
Report Suspected Phishing Attempts: If you receive a suspicious email purporting to be from Apple, report it to Apple’s support team and relevant authorities. This helps them take action to prevent others from falling victim to similar scams.
Deeper Dive into Apple Phishing Tactics
Beyond the general characteristics of phishing emails, it’s essential to understand the specific tactics cybercriminals employ when targeting Apple users:
Impersonation of Apple Services: Phishing emails often mimic the design and language of legitimate Apple communications, making them appear almost identical to authentic messages from the company. Cybercriminals go to great lengths to replicate Apple’s branding, logos, and email templates to enhance the credibility of their scams.
Use of Urgent Scenarios: Phishing emails frequently leverage urgency to manipulate recipients into taking immediate action. For example, they might claim that your Apple account has been compromised and that urgent steps are required to secure it. By creating a sense of urgency, attackers aim to override recipients’ rational thinking and provoke impulsive responses.
Spoofed Links and Websites: Phishing emails often contain links to fake websites that closely resemble legitimate Apple portals. These websites are meticulously crafted to deceive users into entering their login credentials or other sensitive information. Some phishing sites may even feature SSL certificates to give the illusion of security, further deceiving victims into believing they’re interacting with a trustworthy platform.
Social Engineering Techniques: Beyond technical deception, phishing attackers leverage psychological manipulation techniques to exploit human vulnerabilities. They may use emotional appeals, such as fear or curiosity, to persuade recipients to disclose personal information or download malicious attachments. By exploiting human psychology, attackers increase the likelihood of their scams being successful.
Real-Life Examples of Apple Phishing Scams
To illustrate the prevalence and sophistication of Apple phishing scams, let’s examine a few real-life examples:
“Your Apple ID Has Been Disabled” Scam: In this variant, recipients receive an email claiming that their Apple ID has been disabled due to suspicious activity. The email urges them to click on a link to verify their account information and restore access. However, the link leads to a fraudulent website designed to harvest users’ login credentials.
Fake Purchase Confirmation Emails: Cybercriminals send out emails notifying recipients of unauthorized purchases made using their Apple ID. The email includes a link to dispute the charges or cancel the order, but clicking on the link directs users to a fake login page where their credentials are stolen.
Phishing via iCloud Storage Renewal: Attackers exploit users’ reliance on iCloud storage by sending fake emails informing them that their iCloud storage subscription is expiring. The email prompts recipients to click on a link to renew their subscription, leading them to a counterfeit payment page where their financial information is compromised.
Advanced Protection Strategies
In addition to the fundamental precautions mentioned earlier, consider implementing the following advanced protection strategies to enhance your defense against Apple phishing emails:
Email Authentication Protocols: Enable email authentication protocols such as SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) to help verify the authenticity of incoming emails and reduce the likelihood of spoofing attacks.
Email Filtering and Anti-Phishing Tools: Invest in robust email filtering solutions and anti-phishing tools that can identify and block suspicious emails before they reach your inbox. Many email providers offer built-in spam filters, but third-party solutions can provide additional layers of protection.
Continuous Security Awareness Training: Regularly educate yourself and your organization’s employees about the latest phishing tactics and cybersecurity best practices through comprehensive security awareness training programs. Simulated phishing exercises can help reinforce learning and empower individuals to recognize and report phishing attempts effectively.
Monitor for Account Compromises: Keep a close eye on your Apple account activity and set up alerts for any unusual logins or changes to your account settings. Promptly report any suspicious activity to Apple and take immediate steps to secure your account, such as changing your password and enabling two-factor authentication if necessary.
By staying informed about evolving phishing techniques, remaining vigilant against suspicious emails, and implementing robust security measures, you can effectively mitigate the risk of falling victim to Apple phishing scams and safeguard your digital assets and personal information from malicious actors. Remember, proactive defense is the best defense in the ever-evolving landscape of cyber threats.
Related Post:
- Breaking Barriers: Unveiling the Mail’s Journey on Juneteenth
- Mastering Professionalism: Elevate Your Email Game with HubSpot Email Signatures
Apple phishing emails represent a persistent threat to users’ security and privacy, exploiting trust in a reputable brand to deceive unsuspecting individuals. By familiarizing yourself with the red flags of phishing emails and adopting proactive security measures, you can significantly reduce the risk of falling victim to these scams. Remember, staying vigilant and skeptical of unsolicited requests for sensitive information is key to protecting yourself in today’s digital landscape. Stay safe, stay informed, and guard your digital identity with care.